Trezor Login: Secure Access to Your Digital Assets
Master the Trezor login process — your safest gateway to manage, send, and store cryptocurrencies using the world’s leading hardware wallet.
What Is Trezor Login?
Trezor login is a secure authentication method that uses your Trezor hardware wallet to verify identity without revealing private keys online. It replaces the need for passwords with cryptographic confirmation, keeping hackers and phishing attacks at bay.
In simple terms, when you log in through Trezor, your data never leaves your device. You own your keys, your coins, and your privacy.
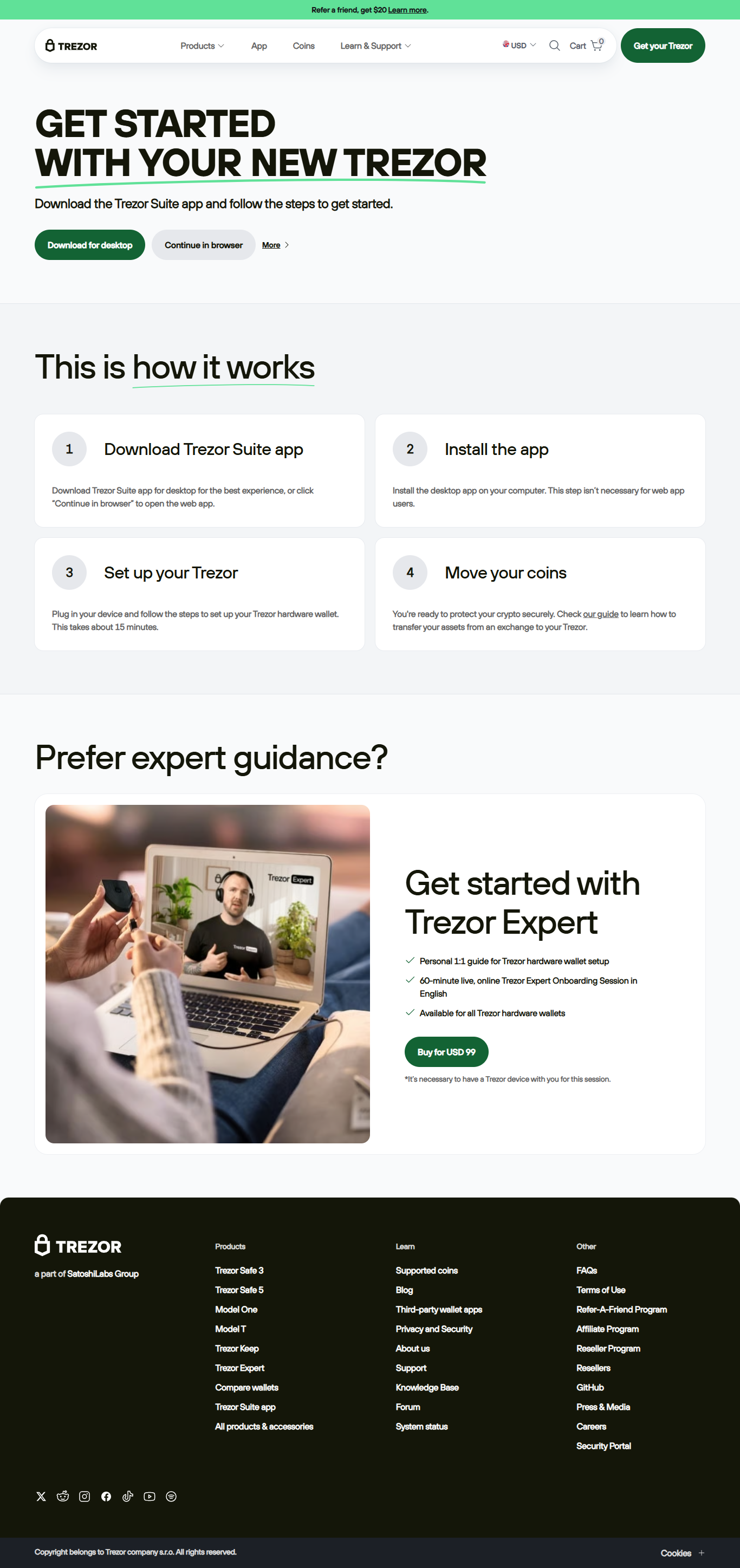
Step-by-Step Guide to Trezor Login
Step 1: Connect Your Trezor
Plug in your Trezor device and make sure your computer recognizes it. Trezor Bridge should be installed and running.
Step 2: Open Trezor Suite
Launch the Trezor Suite desktop app or open the web version. Select “Connect Hardware Wallet.”
Step 3: Authenticate
Review and approve the login request on your device screen. No password or key is transmitted — only a secure signature.
Step 4: Access Your Wallet
Once verified, you can view your portfolio, send coins, or manage your tokens directly from Trezor Suite.
Benefits of Using Trezor Login
- 🔐 Maximum Security: Your private keys never go online — ever.
- 💻 Cross-Platform Access: Works with Windows, macOS, and Linux systems.
- 📖 Full Transparency: Open-source firmware verified by the community.
- 🌍 Universal Compatibility: Connects to various exchanges and wallets seamlessly.
- ⚙️ Continuous Improvement: Frequent updates strengthen protection and usability.
Troubleshooting Trezor Login Issues
Even the most secure devices occasionally encounter login problems. Here’s how to resolve them quickly:
Device Not Recognized
Install or update Trezor Bridge. Use a direct USB port and try a different browser if necessary.
PIN Forgotten
Reset your Trezor device using your 12–24 word recovery seed. This restores access without compromising funds.
Firmware Outdated
Update firmware through Trezor Suite. This enhances performance and maintains compatibility with new coins.
Trezor Login vs Exchange Login
| Feature | Trezor Login | Exchange Login |
|---|---|---|
| Security Level | Hardware-secured, offline | Online, prone to hacks |
| Ownership of Private Keys | You own and control keys | Exchange controls access |
| Login Method | Device verification | Email/password |
| Risk of Phishing | Extremely low | High |
Frequently Asked Questions
1. Do I need internet to use Trezor login?
Yes, but your keys never connect to the web — Trezor signs transactions locally.
2. Can I log in from multiple computers?
Yes, just ensure Trezor Bridge or Suite is installed on each system you use.
3. Is Trezor login safe on public computers?
It’s safer than traditional logins, but avoid public devices to prevent malware risks.
4. What happens if I lose my Trezor?
Use your recovery seed on a new device to restore all your assets securely.
Secure Your Future with Trezor Login
Every time you use Trezor login, you strengthen your control, independence, and security in the crypto space. Protect your wealth — the smart way.